A version of this article was originally published on openSecurity’s monthly Sustainable Security column on 18 November 2014. Every month, a rotating network of experts from Oxford Research Group’s Sustainable Security programme explore pertinent issues of global and regional insecurity.
 This article is part of the Remote Control Warfare series, a collaboration with Remote Control, a project of the Network for Social Change hosted by Oxford Research Group.
This article is part of the Remote Control Warfare series, a collaboration with Remote Control, a project of the Network for Social Change hosted by Oxford Research Group.
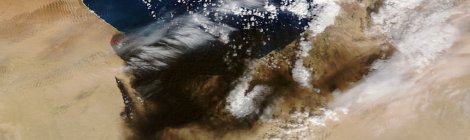
While the world’s attention has been focused on the US-led military interventions in Iraq and Syria a quieter build-up of military assets has been ongoing along the newer, western front of the War on Terror as the security crises in Libya and northeast Nigeria escalate and the conflict in northern Mali proves to be far from over. In the face of revolutionary change in Burkina Faso, the efforts of outsiders to enforce an authoritarian and exclusionary status quo across the Sahel-Sahara look increasingly fragile and misdirected.
The New Frontier
In early August, coinciding with the restructuring of French military operations in the Sahel and the US-Africa Leaders Summit, Oxford Research Group and the Remote Control Project published a comprehensive assessment of counter-terrorist operations targeting jihadist groups in the Sahel-Sahara region of north-west Africa. That report found extensive and growing evidence of combat, intelligence, surveillance and reconnaissance (ISR), training and equipment, abduction and rendition programmes on this new frontier. While France and the US were easily the most active foreign actors, the UK, Canada, the Netherlands and several other NATO states were also found to be increasingly involved in special forces and ISR operations.
The launch coincided with the onset of air attacks on Islamic State targets, initially by the US in northern Iraq and latterly by a broad coalition of Western and Arab states in Iraq and Syria. In a context of worsening security crises in Libya, Nigeria and northern Mali and Niger since, US and UK ISR activity is increasing, French deployments in Mali have been reinforced, a new configuration of Arab states has provided impetus for foreign intervention in Libya’s civil war and a “black spring” backlash is emerging against the west’s authoritarian allies in the region.
Libya on the frontline
Libya is at the core of the security crisis in the Sahel-Sahara. Since the NATO-led military intervention which overthrew the Qaddafi regime in 2011, Libya has become a security and political vacuum and a major exporter of weapons and insecurity in the region. This has included the return home to the Sahel of hundreds of combatants formerly given refuge or employment by the Libyan state.
Libya’s civil war reignited in May with the launch of “Operation Dignity” by secular forces from eastern Cyrenaica, seeking to wrest control of Benghazi and Tripoli, the two main cities, from Islamist militia. This has been largely a failure. Most diplomatic missions evacuated Libya in late July and Tripoli and its burnt-out international airport fell to militia from Misrata (Libya’s third city) and allied Islamist groups on 23 August. Benghazi has fallen increasingly into the hands of Salafist groups and the nearby city of Derna is run as an Islamic emirate by Ansar al-Shari’a. Much of the rest of Libya is dominated by local tribal leaders or armed factions, beyond any state control.

Anti-Gaddafi rebel looks to the sky in the oil town of Ras Lanouf, eastern Libya, March 6, 2011. Source: cropped version of BRQ Network image (via Flickr)
Indeed, there are now two rival, elected Libyan governments. The one recognised internationally meets in a Tobruk hotel. It controls little beyond this Egyptian border outpost and its electoral mandate was recently invalidated by the Tripoli-based Supreme Court. The revived General National Council in Tripoli governs the capital and north-west and is dominated by an affiliate of the Muslim Brotherhood and other Islamist factions.
Libya has thus become a new frontline in the proxy war between the international proponents and opponents of the brotherhood. Qatar and the United Arab Emirates (UAE) were the two main Arab sponsors of the anti-Qaddafi rebellion and contributed to the air attacks on Qaddafi’s forces. They now find themselves backing different sides in Libya. On 17 and 23 August, days after the Tobruk parliament called for foreign military intervention, Emirati aircraft based in and refuelled from Egypt launched unclaimed attacks on pro-Islamist militia around Tripoli airport.
Despite official denials, it appears that air attacks on Salafist groups in Benghazi in mid-October were launched by Egyptian aircraft. Egypt and the UAE accuse Qatar, the primary sponsor of the brotherhood in Egypt, and Sudan, long ruled by a military affiliate of the brotherhood, of funnelling arms to the various Libyan Islamist militias.
While the US has condemned all post-2011 foreign intervention in Libya, it is likely that it was aware of the movement of UAE aircraft to Egypt, given that fighters presumably left from Al-Dhafra air base in Abu Dhabi, which is shared by US and French squadrons. Emirati refuelling aircraft are based at Al-Minhad in Dubai, where the UK Royal Air Force (RAF) has an expeditionary wing. These aircraft presumably were cleared by Saudi Arabia (another great opponent of the brotherhood) to overfly its territory. The aircraft and weapons used were supplied by the US and/or France.
France stands apart among Western allies in its advocacy of, and preparedness for, renewed military intervention in Libya. Since the fall of Tripoli, its defence minister, Jean-Yves Le Drian, has several times advocated a UN mandate for intervention against Islamist groups in Libya and hinted that France may need to act unilaterally sooner or later. Whereas Egypt is most concerned about Salafist groups in Derna and Benghazi, France is focused on al-Qaida affiliates in south-west Libya. Already this year it has opened bases near the Niger-Libya and Chad-Libya borders and revived ISR operations from its air base at Faya-Largeau in northern Chad.
Northern Mali and Niger
France cares about southern Libya primarily because of its security commitments to Mali, Burkina Faso, Chad and Niger, the latter hosting multi-billion-euro French investments in uranium production. Since France reorganised its forces in the Sahel from the Mali-focused Opération Serval to the pan-Sahel deployments of Opération Barkhane in mid-2014, security in northern Mali has worsened significantly. This relates partly to the decline in French troop numbers there but also to the reorganisation of regional jihadist groups and the deterioration in relations between the Malian state and local armed separatists. Twenty UN peacekeepers from the Multidimensional Integrated Stabilisation Mission in Mali (MINUSMA) have been killed in at least five jihadist attacks in the north of the country since September. In response, France has had to reinforce its deployments in Kidal district, pulling in troops and equipment from its base in Côte d’Ivoire.
On 9 October, French forces under Barkhane mounted their first publicly acknowledged offensive action outside of Mali, attacking a convoy supposedly transporting militants and weapons from Libya through Niger towards the country. Militants apparently moving from north-eastern Mali attacked Nigerien security forces in Ouallam three weeks later, freeing dozens of Islamist prisoners and attacking a refugee camp. Citing increased activity, the huge Algerian military is also reported to have moved thousands of troops to its borders with Niger and Mali since last month.
The US has also sought to extend its own ISR deployment in Niger, announcing in early September that it would be moving its two MQ-9 Reaper unmanned aerial vehicles from Niamey airport, where they have been deployed since early 2013, to Agadez, the main town in the desert north. As with French redeployments in 2014, the objective appears to be to bring more of southern Libya into range of ISR assets.
Humanitarian opportunity

RAF Panavia Tornado GR4 fighter over Iraq during a combat mission in support of Operation “Iraqi Freedom”, on 16 August 2004. Source: SSgt. Lee O. Tucker – Official U.S. Air Force Photo no. DF-SD-07-05791 (via Wikipedia)
Perhaps least analysed of recent military deployments to west Africa have been those associated ostensibly with humanitarian, rather than security, crises. In late August, following Boko Haram’s seizure of territory and declaration of its own caliphate in northern Nigeria, the RAF deployed a number (three is reported) of Tornado GR4 aircraft from the UK to the French air base in N’Djamena, Chad. This base is also used by US drones.
Unusually, the Ministry of Defence issued almost no comment on this and refuses to disclose how many aircraft were involved, where they operated from or exactly when and why they were deployed. Officially, they were on an ISR mission in support of attempts to locate the more than 200 girls abducted by Boko Haram from a boarding school in Chibok in north-eastern Nigeria in April. All aircraft had officially returned to the UK by 15 October. While the Tornado GR4 is often deployed as a reconnaissance aircraft, it is dual use and its primary role—for example, in Iraq—is as a medium-range strike aircraft.
Also very little reported was the US Marine Corps’ establishment during September of three new “co-operative security locations” in Senegal, Ghana and Gabon, along the west African coast. These are to be bases permanently prepared and supplied, but not necessarily manned, to support US interventions under the Obama administration’s “New Normal” doctrine, which facilitates defence or evacuation of US interests and citizens under (terrorist) attack in any country. While marines and their V-22 Osprey aircraft may continue to be based in Spain, Italy and Djibouti, these new west African bases are specifically launch pads for future US military interventions. US military contractors have been stockpiling aviation fuel at these and many other African airports for several years.
Interestingly, the Senegal facility has been specifically referred to as an “interim staging base”—the usual terminology for a Special Purpose Marine Air-Ground Task Force base—in the context of the US military’s humanitarian mission to control the Ebola epidemic in Liberia. As with previous Obama-era deployments against the Lord’s Resistance Army in and around Uganda and in support of the Chibok abductees, the escalation of a US military presence appears to have been achieved under the cover of humanitarian imperatives and initiatives.
Towards a Black Spring?
All this matters because if there is one thing that we should have learned since 2001 it is that Western military interventions to oppose terrorism on foreign soil do not work: they tend to destroy the “host” country while amplifying the threat to the “far enemy”. And proxy wars between the Arab states so lavishly armed by the US, France, the UK and Russia tend to end in something worse than tears. Neither the “war on terror” nor the “Arab spring” (counter-)revolution has yet run its course.

“The Army: National Shame” caption held by protester in Mali against the 2012 coup. Source: Wikipedia
The political crisis in Burkina Faso, in which the authoritarian president of 27 years, Blaise Compaoré, was overthrown in a popular uprising turned military coup on 31 October, provides ample warning of the toxic relationships Western states are forging in the Sahel-Sahara in the name of counter-terrorism. As in Mali in 2012, the coup leader in Burkina was an ambitious, US-trained officer. French and US special-operations forces will probably retain their semi-secret bases but their political masters have again been embarrassed by their own role as props to the hated old regime.
Protesters in Burkina Faso—a remarkably civil, peaceful, articulate and internationalist society that belies the Sahel’s reputation for isolation—have talked up the precedent of their revolution for a “black spring” that would sweep away the Western-armed and educated tyrants whose misrule blights the south of the Sahara. They have chosen a very different path to the eschatological nihilism of Boko Haram but their hunger for change is similarly derived from generations of stultifying and systematic marginalisation under a corrupt, militarised and foreign-sponsored elite.
Like Tunisia before it, Burkina Faso may be the clear-sighted vanguard that has the self-belief and self-discipline to manage a successful transition from autocracy. It is hard to hold such hope for the supposedly firmer pillars of western Sahel strategy, Chad and Mauritania, which have known almost nothing but rule by armed clans. Nor for Algeria—where the “printemps noir” epithet was coined during a forgotten 2001 Berber uprising—the last of whose mid-century revolutionary leaders yo-yos, paralysed and dying, between Algiers and French clinics.
Sahara bores are wont to remind outsiders that the great desert is a crossroads, not a cul-de-sac, composed far more of enduring rock than shifting sands. The opposite can perhaps be said of the region’s militaries. Viewed within fragile states, military institutions may look rock-strong but they are built on sand and bound to fickle alliances. As in Burkina, it is society that is the bedrock with the power and permanence to anchor a sustainable strategy for peace and stability.
Trying to contain a revolution in the Sahel-Sahara is not a long-term option but channelling it may be. Change is coming, one way or another.
Richard Reeve is the Director of Oxford Research Group’s Sustainable Security programme. He has researched African peace and security issues since 2000, including work with ECOWAS, the AU and the Arab League.