Often seen as a tactic harnessed by the weak, guerrilla warfare can also be a employed by the strong. States have at times used guerrillas in inter-state and civil conflict.
Guerrilla warfare is widely viewed as a weapon of the weak. To Mao Tse-tung, it was the optimum strategy of those “inferior in arms and military equipment.” He drew inspiration from the Russian troops accomplishing, in 1812, what their militarily superior European counterparts could not: drive Napoleon’s Grand Army out of their country. They did this not only by taking advantage of Russia’s distinctive geography and climate, but also by using guerrillas – Cossacks and peasants – to go after the French troops “as unconsciously as dogs bite to death a rabid stray dog.”
But, guerrilla warfare can also be a weapon of the strong. States with robust conventional military capabilities at times use guerrillas in inter-state and civil conflict.
Guerrilla Warfare

Image by kurdishstruggle via Flickr.
Guerrillas’ advantages stem from their organization and local ties. They typically operate as small, independent units, thereby exercising more maneuverability, alertness, concealment, and access to the local population than their regular counterparts. Carl von Clausewitz recommended supplementing a regular army with bands of armed civilians. He observed that, when faced with adversity, soldiers typically “cling together like a herd of cattle,” while civilians “scatter and vanish in all directions, without requiring a special plan.” But, he emphasized that the latter should not be used “to pulverize the core but to nibble at the shell and around the edges” of regular armies.
Both Clausewitz and Mao viewed guerrillas as useful for weakening a conventionally strong rival through harassment and psychological warfare, but recognized that they are “but one step in the total war.” It is the regular troops that must, in the end, directly confront and defeat the enemy. Thus, for example, the recent U.S. strategy of sponsoring local rebels in Syria against Bashar al-Assad’s (Russia-supported) army was likely to fail not least because of the difficulties inherent in using nonstate proxies. The U.S. strategists – presumed students of Clausewitz – failed to recognize the necessary role of the regular forces, or else significantly underestimated their capacity to form a regular army out of irregulars while in the midst of a war. Or, they were simply constrained by the political unfeasibility of setting regular U.S. soldiers’ boots on the ground.
In addition to weakening (or hopelessly trying to defeat) a rival’s regular forces, states often use guerrillas – or “counter-guerrillas” – against guerrilla rivals. The latter are typically rebels fighting to gain, maintain, or reclaim territorial control from an established government or occupying power. The former are sometimes also referred to as “pro-government militias.”
In a recent article published in the Journal of Strategic Studies, I closely examine and disaggregate the different types of counter-guerrillas states use in counterinsurgency operations. I identify two types of counter-guerrillas: self-defense militias and death squads. Self-defense militias typically comprise ordinary civilians, such as peasants, while death squads are usually manned by experienced militants, such as turned rebels or violent criminals.
I argue that states make proxy choices based on the latter’s comparative advantage, availability, and controllability. The state’s ideal partners are highly skilled fighters with deep knowledge of the insurgent network and links to the local population. Regular soldiers are highly skilled fighters, but possess limited local and insurgent knowledge. Partnering with nonstate actors means tackling the classic principal-agent problem, and the state’s capacity to do so is significantly shaped by its spatial reach (i.e. territorial control) across the theater of war. Figure 1 illustrates the different configurations of territorial control.
Figure 1. Zones of Control
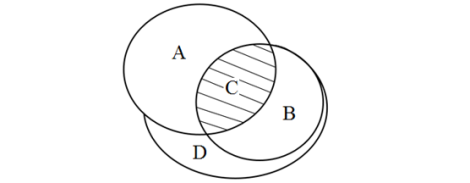
In Zone A, the state exercises full control. Zone B represents the insurgent-dominated area, whereas Zone C is the contested region where both sides actively compete for influence. Zone D represents an area that has been largely neglected in the burgeoning civil war literature. It is a zone that is neither fully controlled nor, for the time being, actively contested.
Among the nonstate alternatives, the ideal partner for the state is a skilled fighter with insider knowledge of the insurgency and its logistics network. The disadvantage of using this type of proxy is that his fighting skills make him dangerous and difficult to control. The cost of losing control of skilled fighters can be unpalatably high. Unless they are weak or collapsed, modern states will prefer to use skilled fighters when and where they can supervise them.
Nonstate actors that possess the desired local knowledge and have significant experience wielding extra-institutional violence, whether of criminal or rebel nature, may be harnessed to counter the insurgents. Their comparative advantage is in performing specialized, offensive, and highly targeted tasks (e.g. assassinations) that take advantage of their high mobility and combat skills. Consequently, they are likely to be used where the insurgents are actually located (Zones B and C). We should expect them in Zone C, where the state can exercise control over their activities. Using death squads in Zone B requires the state to create robust control mechanisms, such as embedding these groups firmly within special operations units of regular military or police forces. Where the state exercises full control (Zone A), or where the insurgents are not yet present (Zone D), states do not require highly targeted offensive operations and, consequently, death squads.
While the comparative advantage of death squads is in highly targeted offensive operations, self-defense militias are best at performing static defensive tasks, such as guarding villages, communication lines, transportation networks, and vital installations. They are, consequently, more likely to be used to facilitate the operation of state forces in contested regions (Zone C) or to deny the insurgency access to areas where neither side has effective control (Zone D). In Zone B, self-defense militias are helpless against the insurgents. Not only can their government-provided weapons easily fall into rebel hands, but also, given the high rates of defection in insurgent-dominated areas, they may become a fertile source of rebel recruits. Remnants of self-defense militias (once created in Zone C or D) may persist in Zone A, but only because demobilization of nonstate actors is usually slow and costly.
The Kashmir Case
India’s use of counter-guerrillas in Kashmir illustrates the logic of the argument. In response to an insurgency breaking out in the late 1980s in the Indian state of Jammu and Kashmir (here referred to as “Kashmir”), the Indian army used former rebels (i.e. “renegades”) and villagers to combat the insurgents. Initial efforts relied on local police enforcement, treating the insurgency as an issue of “law and order.” However, the local policemen proved ineffective and were supplemented by three paramilitary forces (the Central Reserve Police Force, the Border Security Force, and the Indo-Tibetan Border Police). The Indian army’s role expanded further in 1993 with the introduction of the Rashtriya Rifles, an elite army unit created specifically for counterinsurgency operations.
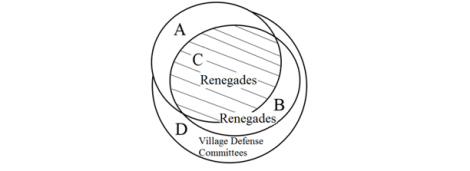
Former rebels were used mostly in the contested areas (Zone C) and, under the supervision of the Rashtriya Rifles, in Zone B. Kashmiri ex-insurgents, who were also popularly known as “Ikhwanis,” were used to eliminate rebels and their sympathizers. In Zone D – the mountainous areas of the Jammu region – the state instituted the civilian-manned Village Defense Committee (VDC) system. Figure 2 illustrates the distribution of the “renegades” and the VDCs. Official statements place the number of VDC volunteers at 6,000, but a prominent Kashmiri journalist I interviewed in Srinagar (the summer capital of Kashmir) estimated the figure to be closer to 23,000.
Figure 2. Zones of Control in Kashmir
Costs of Counter-Guerrillas
Counter-guerrillas may be good for war, but they are bad for peace. Weaponizing turned rebels, criminals, and civilians offers tempting tactical benefits, but it also carries significant post-conflict costs. The conventional wisdom is that outsourcing violence lowers the cost of conflict and provides states with plausible deniability. However, as I learned from my fieldwork in Kashmir and other conflict zones, the local population quickly becomes aware of the illicit links between the counter-guerrillas and the government, as does the international community.
The “renegades” may have helped the Indian army achieve military victory over the insurgents, but they also significantly boosted the widespread and enduring resentment against the Indian government. The arming of a select ethnic group (mostly Hindus and some Sikhs) in Jammu generated “intermittent outburst of communal violence” as well as incidents of looting, abduction, and rape.
Playing local groups against one another is a classic strategy of colonialism, with a lasting impact on the peace and prosperity of many postcolonial states. Perhaps India’s Supreme Court said it best. It described the arming of over 6,000 young men in the tribal tracts by the central Indian state of Chhattisgarh to fight the Naxalite-Maoist insurgents as “tantamount to sowing of suicide pills that could divide and destroy society.”
Yelena Biberman is an Assistant Professor of Political Science at Skidmore College and Nonresident Fellow at the Atlantic Council’s South Asia Center.














